 Verge (XVG) cryptocurrency, which claims to offer features such as anonymity, security, and privacy, is turning out to be more of a joke within the cryptocurrency domain, with a series of 51% attack waged at the will of hackers.
Verge (XVG) cryptocurrency, which claims to offer features such as anonymity, security, and privacy, is turning out to be more of a joke within the cryptocurrency domain, with a series of 51% attack waged at the will of hackers.
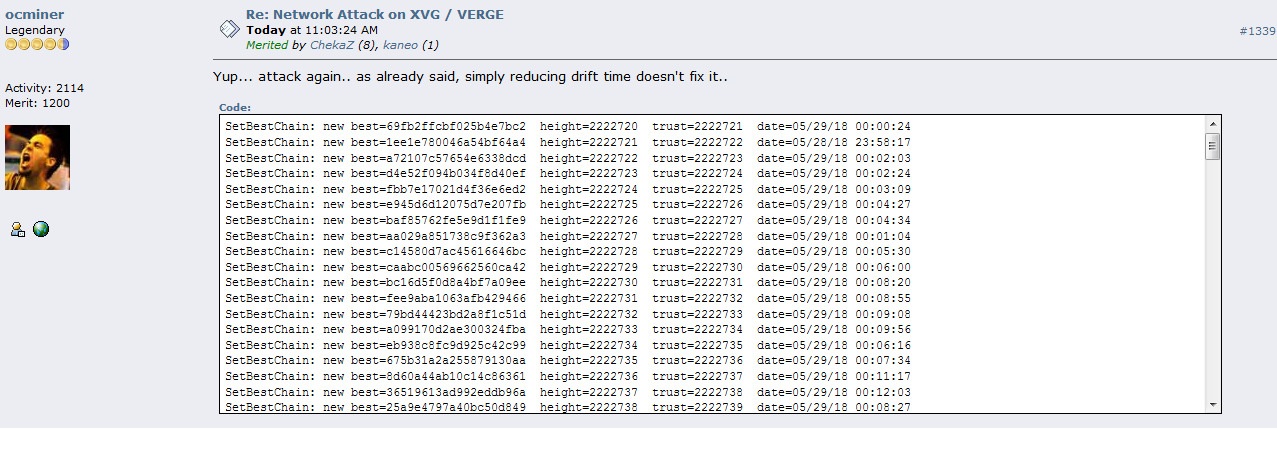
According to a posting made by ‘ocminer’ in the Bitcoin Talk forum, the security of Verge network has been compromised once again. Notably, ‘ocminer’ was the first person to alert about the previous two attacks. Millions of dollars worth Verge (XVG) token was swindled during the past two attacks.
On April 8, we had reported that Verge was subject to a 51% attack that resulted in a loss of 250,000 XVG tokens. Verge responded with a hard fork, but the hacker vouched to come back again to exploit the software bugs. On May 22nd, Verge suffered another hacking incident, almost identical to the previous one.
In the Bitcoin Forum thread titled “Network Attack on XVG / Verge”, “ocminer” says
“Yup… attack again.. as already said, simply reducing drift time doesn’t fix it..”
During the second time, the hacker was able to generate ~35 million XVGs as mining rewards, worth above $1.7 million, using the attack. Following the attack, Verge again implemented a hardfork. However, at that time, Redit user R_Sholes had pointed out that the vulnerability still exists. Again, Verge team downplayed the hacking incident as a “denial-of-service (DDos)” attack on some of the Verge mining pools. However, coding experts had clearly mentioned that it is much more than a simple DDos attack.
How the hacker did it?
Verge uses a different kind of protocol to maintain its network. The protocol known as Dark Gravity Wave difficulty adjustment algorithm automatically adjusts the mining difficulty at the end of every block. Notably, Bitcoin adjusts its mining difficulty at the end of every 2016 blocks. Verge uses five different hashing algorithms (Scrypt, Myr-Groestl, Lyra2Rev2, Blake2s, x17), switching to a new one for every block.
Depending on the use, the hashrate security is split among the algos. Verge, being a decentralized system, allows incorrect time stamping. Last time, this feature of Verge was exploited by the hacker who submitted multiple blocks with incorrect timestamp. The system mistook it as arrival of blocks at a different time and lowered the difficulty by as much as 99.99%. As the hashrate is split among five algos, the hacker was able to reign over the network and directed all the rewards to his own wallet.
During the second time, the hacker attacked two algorithms, Lyra2re and Scrypt, instead of one. The hacker was able to get around the fix put in place last time by Verge team. At the peak of the second attack, the hackers managed to mine 25 blocks (~8250 XVG tokens) per minute.
 United States
United States United Kingdom
United Kingdom















